Online scams have never been more sophisticated, more targeted, or more difficult to detect than they are in 2026. The combination of generative AI, stolen personal data from years of large-scale breaches, and increasingly convincing deepfake technology has fundamentally changed what scam attempts look and feel like. The amateur phishing emails of the early 2010s — riddled with spelling errors, implausible claims, and obvious red flags — have been replaced by hyper-personalised, contextually accurate attacks that fool experienced professionals every day.
This guide covers how the most dangerous scams operating in 2026 actually work — not just what they are called, but the mechanics behind them — and what specific steps you can take to protect yourself, your finances, and your digital identity.
Why Scams Are More Dangerous in 2026 Than Ever Before
Three converging forces have made the scam landscape dramatically more hazardous in recent years.
AI Has Industrialised Personalisation
Until recently, running a personalised scam at scale required significant human effort. Scammers had to research targets, craft individual messages, and manage each conversation manually. Generative AI has collapsed that overhead almost entirely. A scammer with access to basic personal data — name, employer, recent activity, relationships — can now generate thousands of individually tailored phishing messages, voice calls that mimic specific people, and fake documents that pass visual inspection, all at negligible cost.
The practical implication is that the volume of scam attempts has increased dramatically while the average quality of each attempt has improved. You are now statistically more likely to encounter a scam that is specifically relevant to your situation, uses your real name, references real events in your life, and comes from what appears to be a trusted source.
Data Breaches Have Made Personal Information a Commodity
Decades of data breaches — from major incidents at financial institutions, healthcare providers, government agencies, and social media platforms — mean that detailed personal information about most adults is available for purchase on dark web marketplaces at minimal cost. Full name, date of birth, address history, email addresses, phone numbers, financial account numbers, and even social security or Aadhaar numbers are routinely available to anyone willing to pay.
Scammers use this data not just to personalise their approaches but to establish false credibility. When a caller already knows your account number, your last transaction amount, and your registered address, the default human response is to assume they must be legitimate.
The Trust Architecture of Digital Communication Has Weakened
Caller ID can be spoofed. Email sender addresses can be forged. Websites can be cloned pixel-perfect in hours. SMS messages can arrive in the same thread as legitimate messages from a bank. The technical signals that people historically relied on to identify trustworthy communication are no longer reliable, and most people have not updated their mental models to account for this.
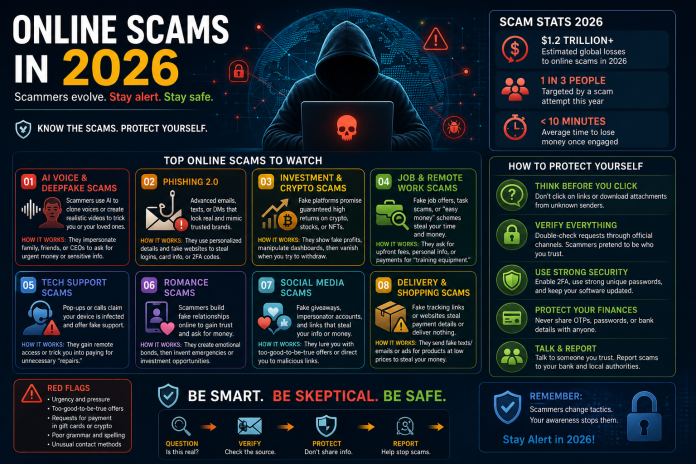
The Most Dangerous Scam Types Operating in 2026
AI-Powered Phishing: The Personalised Threat
Traditional phishing casts a wide net with generic messages hoping for a small percentage of responses. AI-powered spear phishing takes the opposite approach — narrow targeting with highly specific, convincing messages that are far harder to dismiss.
These attacks typically begin with open-source intelligence gathering: your LinkedIn profile, social media activity, any publicly available information about your employer, recent news mentions, or data from previous breaches. The AI then generates an email or message that references specific details of your professional or personal life, creates a plausible scenario requiring action, and directs you to a convincing fake website or requests sensitive information directly.
The defence is not about recognising bad spelling or implausible claims anymore. It is about establishing verification procedures for any request involving credentials, financial transfers, or sensitive data — regardless of how legitimate the request appears. A message that looks exactly like it came from your bank, your employer, or your IT department should be verified through a separate, independently initiated contact before any action is taken.
Deepfake Voice and Video Scams: The Impersonation Evolution
Deepfake technology has matured to the point where real-time voice cloning — generating a convincing imitation of a specific person’s voice from as little as a few seconds of audio — is accessible to anyone with a modern laptop and freely available software. Video deepfakes, while computationally heavier, are viable for pre-recorded scam scenarios.
The most damaging version of this attack in corporate and financial contexts is the CEO fraud deepfake: a voice call or video call appearing to come from a senior executive or trusted person, requesting an urgent wire transfer, credential handover, or sensitive action. Several organisations have lost millions of dollars to exactly this attack pattern.
The individual version targets family members. A cloned voice of a child, sibling, or partner calling to say they are in an emergency and need money transferred immediately bypasses rational scepticism because it triggers an emotional response that overrides analytical thinking.
The protection against this class of attack is establishing pre-agreed verification words or phrases with people you might receive emergency contact from — a family codeword that no AI could know because it was never spoken or written in any digital context. For financial transfers in professional settings, mandatory dual-approval processes and out-of-band verification requirements provide structural protection.
Investment and Cryptocurrency Fraud: The Long Game
Investment scams in 2026 have evolved significantly from the crude “guaranteed returns” pitches of earlier years. The most effective current variant is the “pig butchering” scam (sha zhu pan) — a long-duration social engineering operation in which the scammer builds a genuine relationship with the target over weeks or months before introducing a fraudulent investment opportunity.
The relationship often begins with an apparently accidental contact — a wrong number text, a random connection request, a message on a dating platform. The scammer invests significant time building trust, demonstrating knowledge and apparent success, and eventually introducing an investment platform that shows convincing (but fabricated) returns. Victims are encouraged to invest increasingly large amounts, often liquidating legitimate assets to do so, before discovering that the platform and all its “returns” were entirely fictional and their funds are gone.
The fundamental indicator of this scam type is the combination of unsolicited contact plus investment opportunity introduction, regardless of how long the relationship-building phase lasts. No legitimate investment opportunity requires you to use a specific platform you have never heard of, and no genuine friend or romantic interest will pressure you to invest money.
Identity Theft Through SIM Swapping
SIM swapping is a specific attack that enables access to virtually any account that uses phone-based two-factor authentication. The attacker contacts your mobile carrier, impersonates you using personal information obtained from data breaches or social engineering, and convinces the carrier to transfer your phone number to a SIM card they control. From that point, they receive all SMS messages sent to your number — including the two-factor authentication codes for your email, banking, and investment accounts.
The attack is particularly dangerous because it compromises the secondary factor that most people believe protects them. Once an attacker controls your phone number and has your email password (often obtained separately), they can reset passwords on virtually any account.
Protection requires two steps: using authentication apps (Google Authenticator, Authy) or hardware security keys instead of SMS for two-factor authentication wherever possible, and placing a port freeze or number lock on your mobile account — a feature most carriers offer that prevents number transfers without in-person verification.
QR Code Fraud: The Physical World Attack Vector
QR codes have become a ubiquitous part of daily transactions — restaurant menus, payment terminals, parking meters, advertising — and scammers have adapted by replacing legitimate QR codes with malicious ones that redirect to phishing sites or initiate unauthorised payments.
Physical QR code replacement attacks occur in locations where QR codes are routinely used: parking meters, restaurant table cards, public information displays. A sticker placed over a legitimate QR code is undetectable without close inspection. The redirected URL typically leads to a convincing clone of the expected destination — a parking payment site, a restaurant menu with an embedded payment capture, or a fake banking login.
The habit to develop is checking the URL that a QR code resolves to before proceeding with any action, particularly before entering payment details or login credentials. Most QR scanner apps display the resolved URL before opening it. A parking meter QR code that resolves to a URL unrelated to your city’s parking authority is a clear indicator of fraud.
OTP and Banking Impersonation Fraud
This attack combines social engineering with technical spoofing to extract one-time passwords from victims in real time. The attacker calls using a spoofed number that matches your bank’s legitimate caller ID, claims there is suspicious activity on your account, and walks you through a “verification process” that actually involves providing the OTP your bank just sent you — which the attacker is simultaneously using to authorise an unauthorised transaction.
The defining characteristic of this scam is that your real bank generates a real OTP that the attacker then harvests by convincing you to read it out loud during a call they initiated. The message accompanying most bank OTPs explicitly states that no bank representative will ever ask you to share this code — that instruction exists specifically because this attack is common.
The rule is absolute: no legitimate bank, financial institution, or service provider will ever ask you to read out an OTP during a call they initiated. If this happens, end the call immediately and contact your bank through a number you independently look up.
Building Personal Scam Resistance: Practical Framework
Understanding individual scam types is useful. Having a systematic decision-making framework for any suspicious interaction is more robust, because new scam variants emerge continuously and a principles-based approach protects against attacks that do not yet have names.
The Verification Principle
Any unsolicited communication — regardless of apparent source, regardless of how much personal information the sender demonstrates, regardless of urgency — that requests credentials, financial action, or sensitive information should be verified through an independently initiated contact before any action is taken. You hang up and call back using a number you find yourself. You do not use a callback number the caller provided.
This one principle, consistently applied, defeats the majority of scam attempts regardless of their specific mechanism.
The Urgency Signal
Scammers universally create urgency because urgency bypasses deliberate thinking. “Your account will be frozen in 24 hours.” “This offer expires today.” “Your son has been arrested and needs bail money now.” Any communication that creates pressure to act immediately without time to verify should be treated as a strong indicator of fraud, not as a reason to act faster.
Legitimate institutions — banks, tax authorities, legal entities — communicate in writing, provide reference numbers, allow time to respond, and do not demand immediate action over the phone.
Digital Hygiene as Scam Prevention Infrastructure
Reducing your attack surface requires ongoing hygiene practices: unique, complex passwords for every account stored in a password manager (1Password, Bitwarden, Dashlane); phishing-resistant two-factor authentication on every account that supports it; regular checks of data breach exposure through services like Have I Been Pwned; and minimal public sharing of information that scammers use for personalisation — employer, travel plans, family details, financial activity.
None of these practices individually makes you immune. Together they raise the cost and complexity of targeting you to the point where most opportunistic scammers will target someone with a lower-resistance profile instead.
If You Have Been Scammed: The First 48 Hours
Time is the critical variable in limiting damage from a successful scam. Acting quickly on the correct sequence of steps dramatically improves the probability of recovering funds and preventing secondary damage.
Contact your bank or financial institution immediately and report the fraud. Banks have fraud departments with the ability to freeze accounts, initiate recalls on recent transfers, and flag your account for heightened monitoring. The faster this happens after a fraudulent transfer, the higher the chance of recovery — international wire transfers become significantly harder to reverse after 24–48 hours.
Change passwords for all accounts that share credentials with compromised accounts, prioritising email (which is the master key to most other account recovery) and financial services. Enable two-factor authentication on anything that does not already have it.
Report the incident to the relevant national authority: the Cybercrime Portal (cybercrime.gov.in) and the National Cyber Crime Helpline (1930) in India; the FTC (reportfraud.ftc.gov) and IC3 in the United States. These reports contribute to intelligence that helps law enforcement identify and disrupt scam operations, and a formal report creates documentation relevant to any financial recovery process.
If identity theft occurred — someone used your information to open accounts, apply for credit, or conduct transactions in your name — file a complaint with the relevant credit bureaus to place a fraud alert on your file, which makes it harder for anyone to open new credit in your name.
This article is written for informational and awareness purposes. Cybercrime tactics evolve continuously — if you suspect you are the target of a scam or have been defrauded, contact your financial institution and local cybercrime authorities immediately.